Data Loss Myrtle Beach
Data loss affects every one of us, whether it is through home use or within an enterprise. Data loss is something that no computer user can ignore. It can range from family photos, copies of your resume or essential corporate data.
In each situation, it is serious business.
Being data recovery experts, we have experience in handling data loss on all levels. While managing and recovering lost data is something we can do, we would prefer that you didn’t have to suffer from data loss at all. Let’s take a look at the four main causes of data loss and how they can each be prevented.
Data Loss: Top Causes
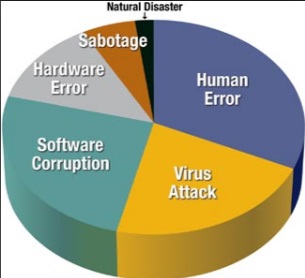
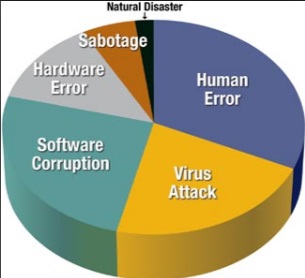
Data loss is very common and varied, but can be categorized into four main areas. The main causes of data loss that we see are:
- Failure of hardware
- Deliberate deletion or theft
- Deletion by accident
- Malware and viruses
Failure of Hardware
When your hardware fails, it can include anything from a hard drive dying to the loss of power to your data source. It can also include events like having your main electricity affected by a storm or spilling that morning coffee onto your laptop.
Deliberate Deletion or Theft
Highly competitive businesses can suffer from industrial espionage, while all businesses can experience the anger of a disgruntled employee. Wiping a system or leaving a time bomb code on a server is something that is very common.
Deletion by Accident
The number one reason we get called for data recovery is deletion by accident. Hitting the delete key when sorting through files or hitting Format when cleaning up the hard drive, deletion by accident occurs every day.
Malware and viruses
With the best software and defenses in place, malware and viruses can still get through and cause many issues with data loss. They can delete your data just because it can and others can hold your data by encrypting it and only giving you the key when you pay.
How to Prevent Data Loss
When it comes to preventing data loss, the task is a twofold process. First, we must protect ourselves from the risk outlined above. Secondly, we need to make sure that despite our best efforts, we have a working copy of the data that you need.
Hardware Maintenance – In order to help prevent data loss, we need to make sure that your computer or server is always kept, cool, free of dust, and maintained on a regular basis. Surge protectors are also a huge help. Using RAID striping across a server can help you survive a hard drive failure as well. Many times, hardware failure is difficult to avoid. Using RAID (Redundant Array of Independent Disks), UPS (Uninterruptable Power Supply) or other mechanical means to keep your system safe is a good idea, but they are by no means foolproof.
Local and Cloud Backup – When it comes to preventing deletion by accident, there is not a lot that we can do except enable shadow copy or File History in Windows 10. This is by no means foolproof, but they are useful in restoring personal computer and office documents. Microsoft Office can also be used to upload copies to Office servers as well as keep local backups. Manually copying your data to cloud storage at the end of your day can be extremely important as well.
Malware and Virus Protection – Quality antivirus and malware programs and a router firewall can help keep malicious codes out of your systems. By using a firewall, you can prevent hackers from gaining access to your computers and servers. This is an essential part of IT security.
A Home user should take advantage of the firewall if it is provided in their ISP modem or router setup. Companies should buy a hardware firewall suitable for the size of the network in order to provide adequate protection for their needs.
Deliberate Deletion or Theft – As we stated before, there is little that you can do in order to prevent the attack of a determined attacker. Restricted logins can help to prevent major damage and RAID will help, but only the use of offsite backups will save you from deliberate deletion or theft.
Backup Solutions That Are Effective and Won’t Break the Bank
Automated backup solutions can cost you thousands of dollars a year, but you may not need to go that route.
Home Users – Important documents can be protected from data loss by utilizing the cloud storage solution. You can copy them manually into the folder or you can use Tech Sentries Backup or other programs to copy that data for you. A failure can occur when you least expect it. It’s a good habit to back up your computer, cellphone, tablet and other devices on a regular basis.
Small business – A home user approach will work great if your business is just you or a few people. Otherwise, there are a few low-cost cloud storage options that will supply you with backup software that will automatically keep your data copied in the cloud storage.
Larger business – Microsoft Azure Storage, EMC and a few others provide enterprise-level backups that are needed for larger businesses. If you need something on this scale, it is very likely that you will have an IT department that can manage this for you.
Preventing Data Loss as a Combined Approach
A two-fold process is needed in order to prevent data loss. It’s important that you do what needs to be done in order to make sure your hardware remains working optimally at all times. Make sure that you secure your machines and network from harm’s way.
Once you have done this, you can then look at the data itself. Keep copies, whether through manual or automatic backups. Also, consider using third party systems such as Tech Sentries Backup to maintain offsite backups. This will ensure that you can quickly recover your lost data should something happen. An effective backup solution is only regarded as effective if you have two copies — the original copy and one in a completely different location. At this point, you can consider yourself well covered!
If you have any questions about preventing data loss or need our help with data recovery, please give us a call. We are here to help you!