In yet another case of “Don’t believe everything you read,” a new ransomware attack has been discovered.
If this image shows up on your computer, the first thing you need to know is that THERE IS NO GOVERNMENT CENTRAL SECURITY TREATMENT ORGANIZATION. You and your computer are being held for ransom.
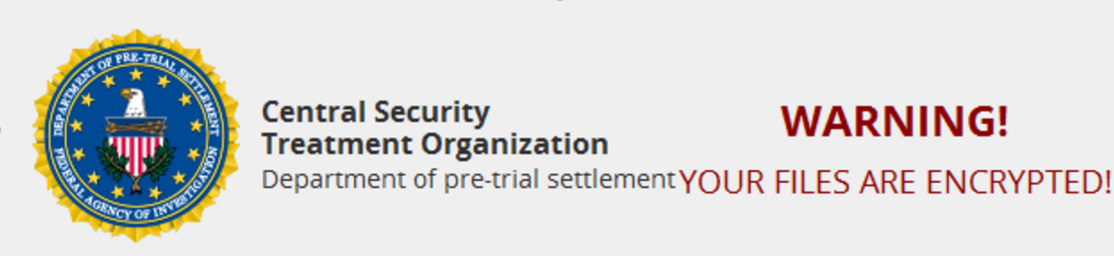
According to one reliable source, the “new ransomware that pretends to be from a fake organization called the Central Security Treatment Organization has been discovered by security researcher MalwareHunterTeam. When the Central Security Treatment Organization ransomware infects a computer it will encrypt a victim’s files and then append the .cry extension to encrypted files. It will then demand approximately 1.1 bitcoins, or $625 USD, in order to get the decryption key.”
The new CryLocker ransomware will
- send information about the victim to the Command & Control server using User Datagram Protocol (UDP).
- use social network site to upload and host information about each of the victims.
- query the Google Maps API to determine the victim’s location using nearby wireless SSIDs.
- stay persistent despite continual reboots
- require a victim’s personal ID information with payment
For those who are wary, but not quite vigilant enough, this ransomware has a special feature designed to “prove” that the organization can unencrypt your computer files. It includes a user demo decryption of a single file. They apparently think that if you don’t fall for trick number one, you might fall for trick number two. These guys are good at understanding human nature too. Then again, we would remind you, “Fool me once, shame on you. Fool me twice, shame on me.” Our goal is for you not to be fooled – ever.
Bleepingcomputer.com has detailed information about CryLocker. KnowBe4 has a free Ransomware Hostage Rescue Manual available to educate consumers and businesses on how to deal with these growing threats.

